Understanding Office 365 identity and Azure Active Directory
Office 365 uses the cloud-based user authentication service Azure Active Directory to manage users. You can choose from three main identity models in Office 365 when you set up and manage user accounts:
-
Cloud identity. Manage your user accounts in Office 365 only. No on-premises servers are required to manage users; it's all done in the cloud.
-
Synchronized identity. Synchronize on-premises directory objects with Office 365 and manage your users on-premises. You can also synchronize passwords so that the users have the same password on-premises and in the cloud, but they will have to sign in again to use Office 365.
-
Federated identity. Synchronize on-premises directory objects with Office 365 and manage your users on-premises. The users have the same password on-premises and in the cloud, and they do not have to sign in again to use Office 365. This is often referred to as single sign-on.
It's important to carefully consider which identity model to use to get up and running. Think about time, existing complexity, and cost. These factors are different for every organization; this topic reviews these key concepts for every identity model to help you choose the identity you want to use for your deployment.
You can also switch to a different identity model if your requirements change.
Watch this video for a quick overview of the different identity models.
You can also use the Azure AD advisors: the Azure AD Connect advisor, the AD FS deployment advisor, the Azure RMS Deployment Wizard, and the Azure AD Premium setup guide.
Cloud identity
In this model, you create and manage users in the Office 365 admin center and store the accounts in Azure AD. Azure AD verifies the passwords. Azure AD is the cloud directory that is used by Office 365. No on-premises servers are required — Microsoft manages all that for you. When identity and authentication are handled completely in the cloud, you can manage user accounts and user licenses through the Office 365 admin center or Windows PowerShell cmdlets.
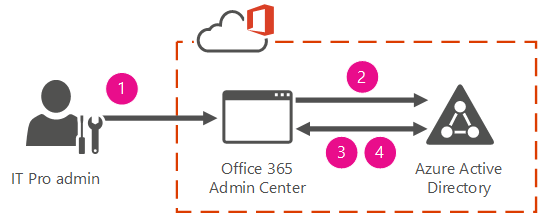
The following figure summarizes how to manage users in the cloud identity model.
In step 1, the admin connects to the Office 365 admin center in the Microsoft cloud platform to create or manage users.
In step 2, the create or manage requests are passed on to Azure AD.
In step 3, if this is a change request, the change is made and copied back to the Office 365 admin center.
In step 4, new user accounts and changes to existing user accounts are copied back to the Office 365 admin center.
When would you use cloud identity? Cloud identity is a good choice if:
-
You have no other on-premises user directory.
-
You have a very complex on-premises directory and simply want to avoid the work to integrate with it.
-
You have an existing on-premises directory, but you want to run a trial or pilot of Office 365. Later, you can match the cloud users to on-premises users when you are ready to connect to your on-premises directory.
To get started with cloud identity, see Set up Office 365 for business – Admin Help.
Integrating Office 365 with a directory service
If you have an existing directory environment on-premises, you can integrate Office 365 with your directory by using either synchronized identity or single sign-on and federated identity to create and manage your users in Office 365.
Synchronized identity
In this model, you manage the user identity in an on-premises server and synchronize the accounts and, optionally, passwords to the cloud. The user enters the same password on-premises as he or she does in the cloud, and at sign-in, the password is verified by Azure AD. This model uses a directory synchronization tool to synchronize the on-premises identity to Office 365.
To configure the synchronized identity model, you have to have an on-premises directory to synchronize from, and you need to install a directory synchronization tool. You'll run a few consistency checks on your on-premises directory before you sync the accounts.
When to use synchronized or federated identities:
| This model: | Works in these situations: |
| Synchronized identities | When you have an on-premises directory and you want to synchronize user accounts and optionally passwords. If you also synchronize passwords, your users will use the same password to access on-premises resources and Office 365. When you ultimately want federated identities, but you are running a pilot of Office 365 or, for some other reason, you aren't ready to dedicate time to deploying the Active Directory Federation Services (AD FS) servers yet. |
| Federated identities | When you need an advanced scenario, such as: existing federation, policy, or technical requirements (more information under Federated identity). |
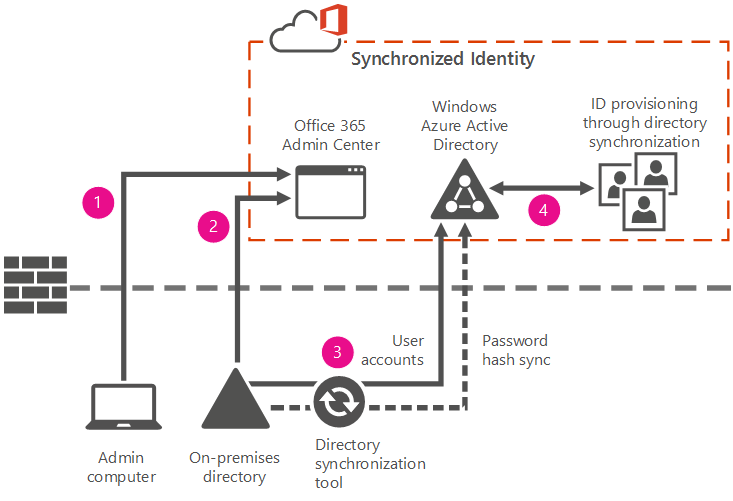
The following diagram shows a synchronized identity scenario with a password synchronization. The synchronization tool keeps your on-premises and in-the-cloud corporate user identities synchronized.
In step 1, you install a Microsoft Azure Active Directory Connect. For instructions, see Set up directory synchronization in Office 365. For more information about Azure Active Directory Connect, see Integrating your on-premises identities with Azure Active Directory.
In steps 2 and 3, you create new users in your on-premises directory. The synchronization tool will periodically check your on-premises directory for any new identities you have created. Then it provisions these identities into Azure AD, links the on-premises and cloud identities to one another, synchronizes passwords, and makes them visible to you through the Office 365 admin center.
In step 4, as you make changes to the users in the on-premises directory, those changes are synchronized to Azure AD and made available to you through the Office 365 admin center.
To get started with synchronized identity, see Prepare to provision users through directory synchronization to Office 365, and Set up directory synchronization in Office 365.
Federated identity
This model requires a synchronized identity but with one change to that model: the user password is verified by the on-premises identity provider. This means that the password hash does not need to be synchronized to Azure AD. This model uses Active Directory Federation Services (AD FS) or a third-party identity provider.
The reasons for using a federated identity include:
-
Existing infrastructure
If you already have AD FS deployed for some other reason, you will likely want to use it for Office 365 also.
If you already use some other identity provider, you will want to use federated identity with Office 365. Microsoft provides a list of identity providers that work with Office 365.
If you use Forefront Identity Manager, you will also want to use federated identity with Office 365.
-
Technical requirements
You have multiple forests in your on-premises Active Directory Domain Services (AD DS).
You have an on-premises integrated smart-card solution.
You have an existing custom hybrid application, for example with SharePoint or Microsoft Exchange Server.
-
Policy requirements
You require sign-in audit and/or immediate disable.
You require single sign-on.
You have sign-on restrictions by network location or work hours.
You have other policies in place that require federated identity.
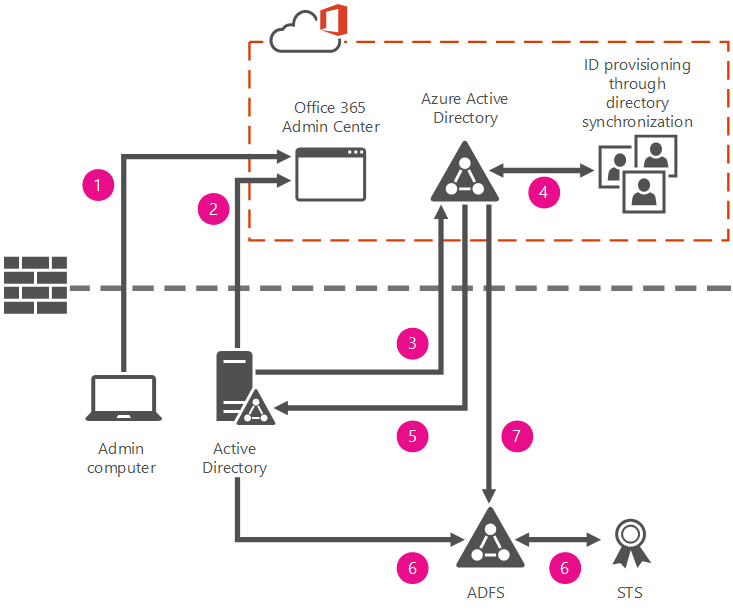
The following diagram shows a scenario of federated identity with a hybrid on-premises and cloud deployment. The on-premises directory in this example is AD FS. The synchronization tool keeps your on-premises and in-the-cloud corporate user identities synchronized.
In step 1, you install Azure Active Directory Connect (find more information and download instructions here). The synchronization tool helps to keep Azure AD up-to-date with the latest changes you make in your on-premises directory.
For instructions, see Set up directory synchronization in Office 365. Specifically, you will need to use a custom install of Azure AD Connect to set up single sign-on.
In steps 2 and 3, you create new users in your on-premises Active Directory. The synchronization tool will periodically check your on-premises Active Directory server for any new identities you have created. Then it provisions these identities into Azure AD, links the on-premises and cloud identities to one another, and makes them visible to you through the Office 365 admin center.
In steps 4 and 5, as changes are made to the identity in the on-premises Active Directory, those changes are synchronized to the Azure AD and made available to you through the Office 365 admin center.
In steps 6 and 7, your federated users sign in with your AD FS. AD FS generates a security token and that token is passed to Azure AD. The token is verified and validated and the users are then authorized for Office 365.
Azure Active Directory management portal
If you have a paid subscription to Office 365, Microsoft Dynamics CRM Online, Enterprise Mobility Suite, or other Microsoft services, you have a free subscription to Azure AD. Although you can use Azure AD to create and manage user and group accounts, it's a good idea to you use the Office 365 admin center. For example, even if you can add users in the Azure management portal, you still need to add licenses in the Office 365 admin center. You have to activate your subscription to access the Azure management portal.
For more information see Azure AD Connect FAQ
No comments:
Post a Comment